Retroactive Settlement Verification
Every historical payment, re-verified.
100 million records in 10 to 20 minutes. The corpus is replayed through the vendor's Tier 1 profile (a required subset of the 175 check catalog); Ava determines which fraud-detected settlements are warranted beyond Tier 1; the customer approves or ignores. Sealed CREB™ ships only on approved findings; the corpus-level Merkle root anchors on JIL L1.
What this pillar does for you.
Retroactive Verification is the cleanest description of what JIL does for historical payments: you give us your past payment history, we run 175 checks across free public data + your records, and we tell you which payments were improper, fraudulent, or recoverable - with sealed evidence per finding. For an MCO, that's hitting the CMS 60-Day Rule with documented detection. For a state Medicaid program, it's identifying recovery candidates without contingency-fee exposure. For a federal agency, it's the audit trail that survives an OIG referral.
If you're a Medicaid MCO worried about the 60-Day Rule
Once you "have identified or had reason to identify" an overpayment, you have 60 days under the False Claims Act to report and return - or you're knowingly concealing. JIL gives you the documented detection + substantiation + sealed evidence inside the window. CREBs deliver per case in days; counsel files inside 60 days; you stay in safe harbor.
If you're a state Medicaid program with $50-80B annual loss
JIL runs your historical claims against the 175-check catalog. Surfaces excluded providers re-emerging under new tax IDs, multi-state UBO rings, premise-business mismatches, phantom telehealth, kickback patterns. Sealed evidence per finding. Recovery referrals to your fraud unit or to the state AG's office. Fixed-fee, not contingency.
If you're a federal IG or OIG
JIL processes years of historical disbursements at scale (100M records in 10-20 minutes). Surfaces the patterns your manual audit can't see in time: cross-agency duplicates, beneficial-owner overlap with debarred contractors, cross-program identity fraud. Sealed evidence per finding admissible in administrative hearing, civil enforcement, or criminal referral.
What you get back: a structured findings package with severity bands, sealed evidence per finding (CREB™ - Court-Ready Evidence Bundle), source provenance for every flag, and a recovery-priority list. Findings deliver in days, not months. See the Tier flow visual for how Retroactive runs through Tier 1 → Ava → Tier 2 → Ava Pro → Tier 3 → Ava Pro+.
One corpus in. A ranked, sealed findings ledger out.
Customer ships a 4-year payment corpus. JIL re-verifies every record against the vendor's Tier 1 profile, Ava surfaces Tier 2 fraud-detected settlements, the customer approves or ignores, and CREB™ ships only on the approved findings. Funds already moved - JIL re-verifies the record, not the rail.
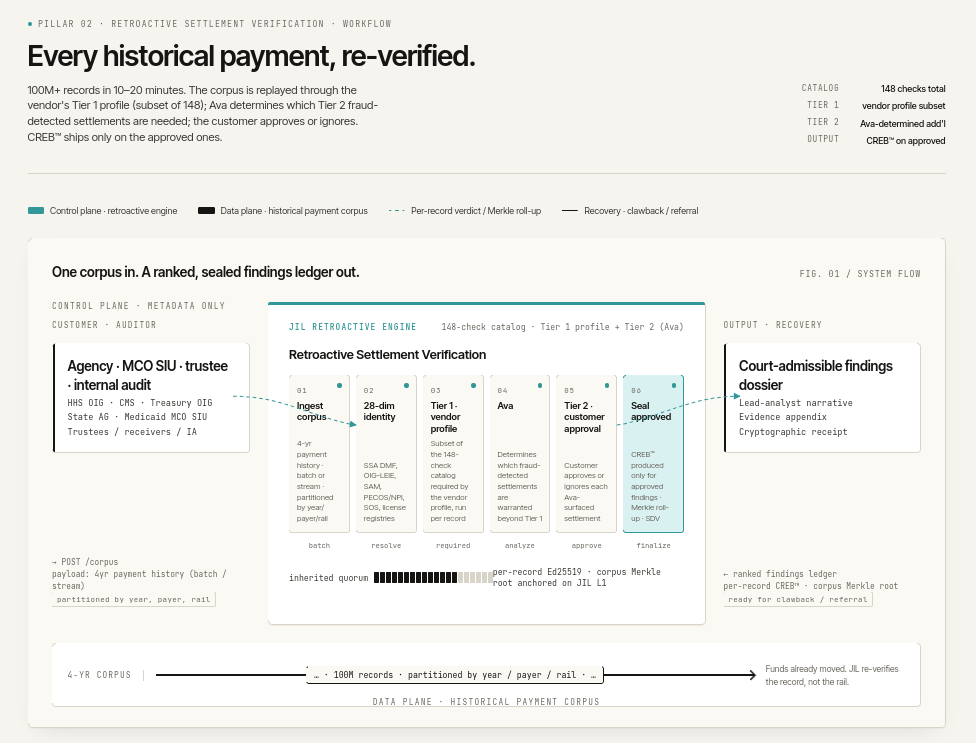
Control plane and data plane are strictly separated.
JIL operates the retroactive attestation engine. The customer keeps custody of the historical payment corpus. The corpus arrives as metadata only - no PHI, no PII bulk, only the surface needed to verify each record. JIL re-verifies and produces sealed findings; recovery (clawback, referral) is the customer's downstream action.
Retroactive engine
- 175 check catalog. Tier 1 = the required vendor-profile subset that runs per record; Tier 2 = additional fraud-detected settlements Ava determines are warranted beyond Tier 1.
- 28-dim identity resolution against authoritative registries: SSA DMF, state death records, OIG-LEIE, SAM debarment, PECOS / NPI, SOS dissolution, license revocations, address vitals, and 20 more.
- Per-record Ed25519 verdict; corpus-level Merkle root signed by 14-of-20 SCN BFT and anchored on JIL L1.
- Inherited-quorum architecture (patent claim 51): the corpus signature inherits the per-record verdicts via the Merkle root, so a single L1 anchor evidences all 100M records.
- Customer approval gate: CREB(TM) is produced only on findings the customer approves. Ignored items leave no signed artifact.
Historical payment corpus
- The customer's existing payment store: claims warehouse, ACH ledger, wire log, RTP archive, on-chain history.
- 4-year corpus by default; configurable per regulatory regime.
- 100M+ records partitioned by year, payer, and rail. Canonicalized into a normalized record schema before re-verification.
- Funds already moved. JIL re-verifies the record, not the rail.
- Recovery is the customer's downstream action: clawback, referral, civil filing, regulator self-disclosure, internal corrective action.
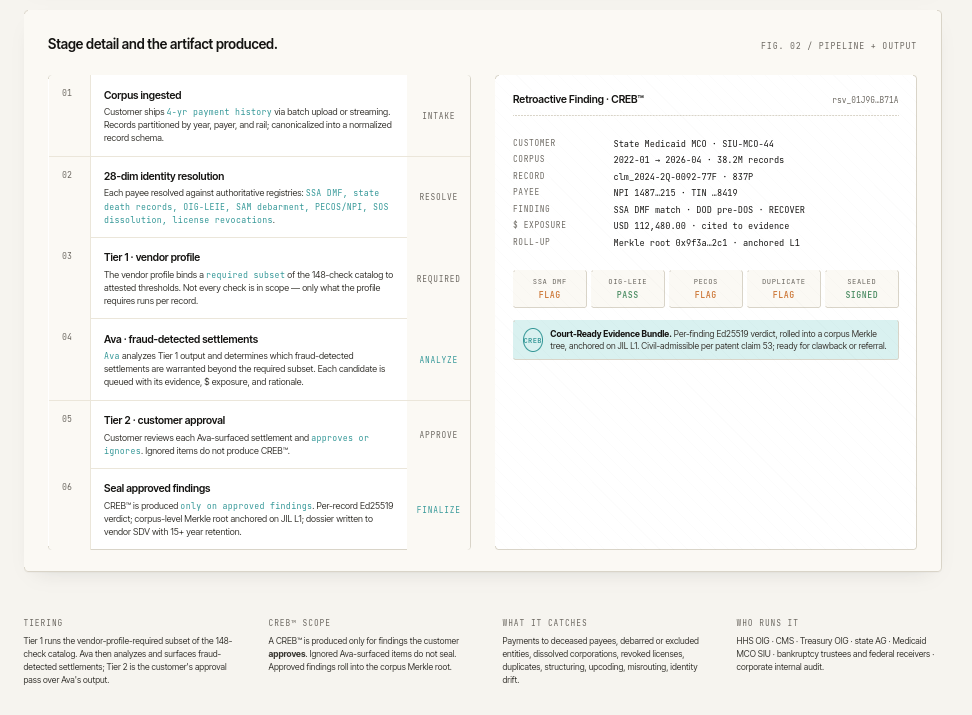
Six stages from corpus to sealed findings ledger.
Stages 02 and 03 run in massively-parallel sharded execution against the corpus. Stage 04 (Ava) is agentic - it reasons over Tier 1 output to identify which fraud-detected settlements warrant escalation. Stage 05 is the customer's approval gate. Stage 06 only runs on approved findings.
Corpus ingested
Customer ships 4-year payment history via batch upload or streaming. Records partitioned by year, payer, and rail; canonicalized into a normalized record schema. Metadata only - no PHI, no PII bulk traverses the network.
28-dim identity resolution
Each payee resolved against authoritative registries: SSA DMF, state death records, OIG-LEIE, SAM debarment, PECOS / NPI, SOS dissolution, license revocations, address vitals, NPPES, sanctions lists, and more. Resolved across 28 dimensions per payee.
Tier 1 - vendor profile
The vendor profile binds a required subset of the 175 check catalog to attested thresholds. Not every check is in scope - only what the profile requires runs per record. Massively parallel sharded execution; 5K-50K records / sec sustained.
Ava - fraud-detected settlements
Ava analyzes Tier 1 output and determines which fraud-detected settlements are warranted beyond the required subset. Each candidate is queued with its evidence, dollar exposure, and rationale. Ava recommends; Ava does not seal.
Tier 2 - customer approval
Customer reviews each Ava-surfaced settlement and approves or ignores. The approval gate is mandatory: ignored items do not produce a CREB™. Approved items move to Stage 06 for sealing. The customer's policy decides.
Seal approved findings
CREB(TM) is produced only on approved findings. Per-record Ed25519 verdict; corpus-level Merkle root anchored on JIL L1 with 14-of-20 BFT quorum signature. Findings dossier written to vendor SDV with 15+ year retention.
Vendor profile subset
Runs per record across the entire corpus. The vendor profile binds a deterministic subset of the 148 catalog checks. Per-record verdict; Merkle roll-up.
Fraud-detected settlements
Determines which additional cases warrant escalation. Outputs ranked candidates with evidence, dollar exposure, and rationale. Recommends; does not seal.
Customer approval
Approve / ignore on each Ava-surfaced settlement. CREB™ ships only on approved. Ignored items leave no signed artifact - the customer remains in control of the public record.
Your LOB. Your tier. Your checks. Ava data-mines only what you approved.
175 production checks live today (and growing). JIL ships a default profile per Line of Business at each tier (1, 2, 3); customers customize from there. Ava's retroactive sweeps run only over the checks you have enabled, and the reproducibility manifest in every CREB™ carries your profile_id + check-set hash so a third party replaying the analysis gets bit-identical results.
| LOB (Line of Business) | Tier 1 - public-data baseline (included in your engagement) | Tier 2 - + commercial enrichment (scoped per case) | Tier 3 - + investigator + court-gated (premium, sealed CREB™) |
|---|---|---|---|
| Managed Care Org. (MCO) | ~39 checks (DRG outlier, NPI/HCPCS anomaly, OFAC/OIG LEIE, NPPES, POS, geo, CERT) | + UBO graph, premise verification, commercial corporate registries | + bank fingerprint, investigator review, court-order-gated |
| P&C Insurance | ~14 checks (OFAC, OpenSanctions, GLEIF, geo outlier, state SoS basic) | + UBO graph, premise verification, LexisNexis address | + bank fingerprint, investigator review |
| Bankruptcy Trustee | ~18 checks (OFAC, EDGAR, FAA aircraft, NFTL, geo) | + UBO graph (depth 3), FinCEN BOI, tax-form gating | + subpoena-gated sealed instruments, sealed CREB™ |
| Federal Investigator | ~32 checks (OFAC + UN + EU + UK consol., OIG, NPPES, CERT) | + UBO graph, premise, sanctions deep, commercial corp registries | + court-order-gated, sealed CREB™, investigator |
| Crypto Exchange | ~12 checks (OFAC SDN, address screening, statistical wallet outliers) | + UBO graph, address co-location, mixer detection | + sealed verdict for examiner defense |
| Stablecoin Issuer | ~10 checks (OFAC, EU MiCA basics, statistical issuance) | + UBO graph, jurisdiction-by-jurisdiction enrichment | + sealed verdict for compliance audit |
The 175 check catalog is the universe; LOB-default Tier 1 picks the public-data baseline subset (included in your engagement), Tier 2 layers in commercial enrichment (scoped per case), Tier 3 adds the bank graph + investigator review + court-order-gated sources.
Customer customization (opt-out of specific checks within the tier) is audit-logged. The customer's profile_id is embedded in every CREB™'s reproducibility manifest, so the same corpus + the same profile produces the same findings ledger, every replay.
No external LLM. No data exfiltration. Findings you can defend in a hearing.
Ava is JIL's in-house Agentic AI + Data Mining engine. No OpenAI API. No Anthropic API. No Google Vertex. The model, the orchestration, and the data-mining queries all run on-premise inside JIL's perimeter (or, on customer engagement, inside the customer's tenant). Customer data never leaves the customer's perimeter. The Tier 1 verdict path is deterministic rules + statistics, not stochastic LLM inference; Ava's agentic layer rides on top to group, narrate, and route findings but never produces the underlying flag.
Same input - same finding, every run. Verdict path uses rules + statistics, no stochastic LLM.
No flag without z >= 3 + >= 2 corroborating signals. Reason codes are first-class fields.
HIGH (z >= 4 + 3 sigs) / MEDIUM (z >= 3 + 2 sigs) / LOW (single-signal). Filter for legal review.
Drill from finding to constituent rows. CREB™ evidence matrix shows exactly which check fired.
Customer marks false-positive - updates Ava's suppression ledger. Original finding never deleted, only annotated.
CREB™ - Court-Ready Evidence Bundle.
Sealed only on approved findings. Per-claim, per-payer, per-payee, with the full check rendition + Ava's escalation rationale + the customer's approval signature. The corpus-level Merkle root anchors all per-record verdicts in a single L1 transaction (inherited-quorum, patent claim 51). Civil-admissible per FRE 902(14) and patent claim 53.
| RSV | rsv_01J9G...B71A |
| Customer | State Medicaid MCO - SIU-MCO-44 |
| Corpus | 2022-01 to 2026-04 - 38.2M records |
| Record | clm_2024-2Q-0092-77F - 837P |
| Payee | NPI 14...215 - date-of-service 2024-04-18 |
| Tier 1 verdict | FLAG - LIC-04, EXC-02 |
| Ava rationale | License revoked 2024-03-22 |
| $ exposure | USD 48,712.00 |
| Customer decision | APPROVE for clawback |
| Per-record sig | Ed25519 - corpus root anchored |
| L1 anchor | jil-l1 - block 18,902,441 |
| Retention | 15 yr - SDV |
A FLAG with a Tier 1 license-on-date violation (LIC-04) plus an exclusion-list match (EXC-02) was caught against a date-of-service of 2024-04-18, when the payee's license had been revoked on 2024-03-22. Ava surfaced the finding with the underlying chain-of-custody. The customer's SIU approved for clawback - the CREB™ is now the supporting evidence for that recovery action.
The corpus-level Merkle root anchors the per-record verdicts in a single L1 transaction. This means the 38.2M-record corpus has one cryptographic provenance event on JIL L1, not 38.2M. The CREB™ references that anchor, and any third party can re-verify any record's verdict against the published Merkle path - without JIL Sovereign's cooperation.
Who runs this pillar, and against what corpus.
Retroactive Settlement Verification is a single pipeline; the vendor profile loaded at Stage 03 specializes the verdict to the customer's recovery context. Federal/state enforcement agencies, MCO payment-integrity teams, qui tam relator counsel, court receivers, and internal audit all use the same engine - different profiles, different recovery downstream actions.
Special Investigations Unit
4-year claim corpus replayed for fraud / waste / abuse. Tier 1 catches license-on-date, exclusion, and corridor outliers; Ava surfaces fraud-detected settlements. Approved findings feed payment integrity recovery and SIU referrals.
Federal program integrity
Replay Medicare and Medicaid claim corpus for improper payments. Per-record CREB™ feeds CMS recoveries, HHS-OIG audits, and DOJ Civil Frauds (FCA / qui tam). The corpus Merkle root is the single audit-trail anchor.
Original-source documentation
Replay the pre-discovery corpus available from public + relator-disclosed data. Ava's escalation rationale + the customer's approval is the structural advantage for original-source defenses under 31 U.S.C. § 3730(e)(4).
Improper-payment review
Federal disbursement programs (SBA, HUD, USDA, IRS refunds) replayed for improper payments. Ava clusters by typology (death-master, dissolved entity, ineligible recipient). Approved findings feed Treasury recovery + GAO reports.
Civil recovery actions
Court receivers, judgment-execution counsel, state AG civil divisions replay defendant payment history for hidden-asset traces. Pillar 03 (Asset Intelligence) extends the surface; Retroactive supplies the historical-payment baseline.
Self-disclosure prep
Pre-litigation self-disclosure under DOJ self-disclosure guidance. Replay 4-year corpus, identify exposure, approve findings the customer is prepared to disclose. The CREB™ is the supporting evidence in the disclosure submission.
100M records in 10 to 20 minutes.
The retroactive engine is throughput-bound, not latency-bound. The pipeline is shardable across the 20-validator pool; per-record signatures aggregate via inherited-quorum (patent claim 51) into a single corpus Merkle anchor.
| Metric | Target (Phase 1) | Phase B (post-BLS + sharding) |
|---|---|---|
| Corpus throughput - 100M records | 10-20 minutes | 2-4 minutes |
| Per-record sustained verdict rate | 5K-50K records / sec | 200K-500K records / sec |
| Identity resolution (28-dim per payee) | 30-100 ms cached, 300-800 ms cold | same; cache hit-rate 90%+ steady-state |
| Ava analysis throughput | 10K candidates / sec | 50K+ candidates / sec |
| BFT quorum | 14 of 20 (corpus root); per-record Ed25519 | same; BLS aggregate at the corpus level |
| CourtChain™ anchoring | 1 anchor per corpus (Merkle root) | same; no per-record anchor required |
| CREB™ issuance latency (per approved finding) | < 5 s | < 1 s |
| Customer approval gate | customer-paced; queue persists | same |
| Availability | 99.5% | 99.95% |
| Retention | 15+ years on the customer's SDV; CourtChain™ anchor permanent | |
Ship the corpus. Approve the findings. Recover.
Two endpoints: POST /v1/retroactive/corpus to ingest (batch or streaming) and POST /v1/retroactive/findings/:id/decision to approve or ignore Ava-surfaced settlements. Same dual-path auth as the rest of the JIL stack: HMAC-signed primary, mTLS at the edge for institutional, Bearer for admin / cron.
POST /v1/retroactive/corpus
X-JIL-Access-Key-Id: rsv_a3f9b7c2
X-JIL-Timestamp: 2026-04-29T17:32:08Z
X-JIL-Nonce: <16+ bytes opaque>
X-JIL-Signature: base64( HMAC-SHA256(secret, canonical) )
Content-Type: application/x-ndjson
{ "record_id": "clm_2022-1Q-0001-0F", "payer": "MCO-HM-44", "payee_npi": "1487...215",
"amount": "612.50", "rail": "ACH", "date_of_service": "2022-01-04",
"issued_at": "2022-01-08T09:14:22Z" }
{ "record_id": "clm_2022-1Q-0001-10", ... }
... 38,200,000 more records ...
{
"rsv_id": "rsv_01J9G...B71A",
"corpus_window": { "from": "2022-01-01", "to": "2026-04-28" },
"estimated_records": 38200000,
"tier_1_profile": "mco-payment-integrity-v3",
"status": "running",
"progress_url": "/v1/retroactive/rsv_01J9G...B71A/progress",
"ava_settlements_url": "/v1/retroactive/rsv_01J9G...B71A/findings"
}
POST /v1/retroactive/findings/find_01J9G_4F2A1/decision
{ "decision": "approve", "downstream_action": "clawback", "notes": "..." }
200 OK
{ "creb_id": "creb_01J9G...B71A_4F2A1",
"creb_url": "sdv://customer-44/creb/creb_01J9G...B71A_4F2A1.pdf",
"anchor": { "chain": "jil-l1", "block": 18902441, "merkle_path": "..." } }
EVERY API call is authenticated and attributed via billing.api_keys + billing.customers. Every request writes a row to billing.audit_log. Customer-id is the primary key for privacy (a customer can only see their own corpus jobs and findings) and revenue tracing. The same auth + attribution model as Pre-Settlement Attestation and JIL Corridor.
Questions answered by the retroactive engine.
- Was the payee dead on the date of service? SSA DMF + state vitals death verification, evaluated at the payment date.
- Was the payee excluded? OIG-LEIE, SAM, state Medicaid exclusion, corporate-integrity-agreement status, debarred contractor lists - evaluated as of the historical date.
- Was the license valid on the date of service? NPPES + state licensing + DEA registration + facility certification, against the relevant historical date - not today.
- Was the entity dissolved? SOS dissolution records, registry status, name-change pivot detection, shell-entity flags.
- Is the payee a duplicate enrollment? Cross-program / cross-jurisdiction duplicate detection (state Medicaid, Medicare, Tricare, VA).
- Are the corridor / typology / velocity patterns anomalous? Tier 1 thresholds applied per-record; Ava clusters anomalies into actionable settlements.
- Should this finding be approved for recovery? Ava recommends, the customer approves; CREB™ ships only on approved.
One pipeline. Six delivery surfaces.
Pre-Settlement
Decide before the money moves.
Asset Intelligence
Find, trace, and seal verdicts on hidden assets.
Wallet Intelligence
42 signals. One verdict. Under 200 ms.
Pre-Clearance
The SWIFT for crypto.
Institutional Wallet
The safe-passage delivery surface.
Ready to replay your 4-year corpus and recover what slipped through?
Engagement framework, vendor-profile design, and integration runbook are available under NDA. Initial briefings are 60 minutes for federal / state enforcement, payer SIU, qui tam relator counsel, court receivers, and internal audit.